Cyber Security
Protecting your team and business from digital threats
In the ever-changing digital world, it’s more important than ever to secure your tech. This collection teaches you how to mitigate cyber threats and secure your data from theft and corruption. Add cybersecurity skills to your skill set.

Benefits
A comprehensive collection
Explore 25+ courses, covering GDPR to phishing. Dive into diverse content on cyber security to safeguard yourself and your business from potential threats.
IOSH & CPD certified learning
This collection contains courses which are fully certified by IOSH, and all by the CPD Certification Service – so you can be assured gold-standard content which is both accurate and useful.
Learn in minutes, not hours!
Quick and engaging courses that can be taken in just 5-15 minutes, enabling rapid upskilling and improving learner retention. Plus, learn from anywhere, on any device!
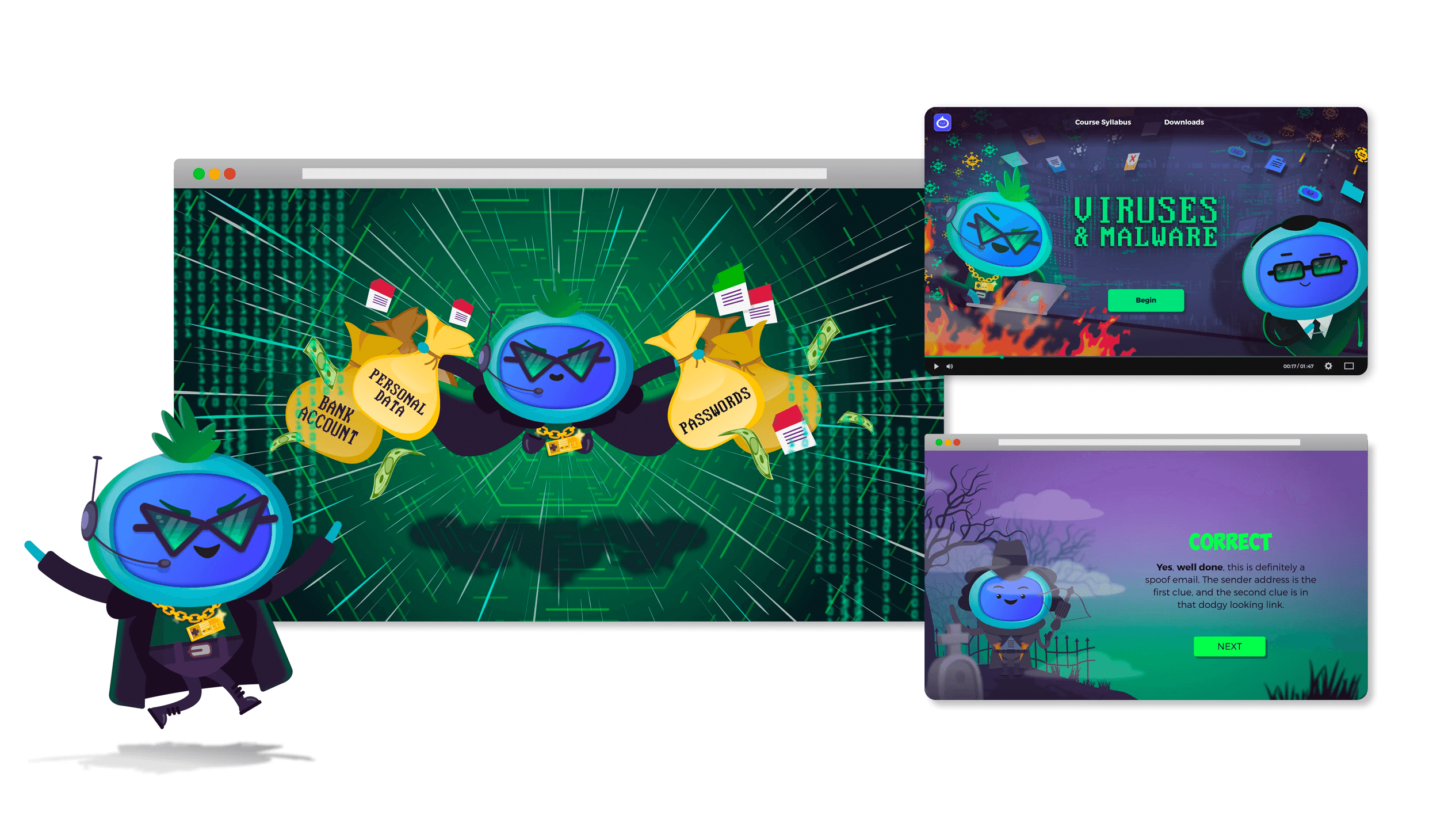
Keep learners engaged
The courses use captivating storytelling, animation, and interactivity, so learners are more likely to retain information and convert that into practical change.
A glimpse at some of the courses
Train yourself to keep that tech under your control and stop hackers in their tracks with our engaging, up-to-date cyber security collection. These courses cover a myriad of topics, including email security, phishing, viruses & malware, using a strong password, and spoofing attacks. These courses use clear language - no unexplained jargon – and are designed to help keep you compliant with GDPR rules.










Search our Cyber Security courses
There are no courses that matches your search criteria
Please try adjusting your search terms or removing filters to broaden your search criteria
Loading...

Want to see more?
Your business will likely face unique challenges, but our friendly team is happy to answer any questions you may have. We’re eager to show you any specific courses you’re interested in, or guide you through our off the shelf eLearning courses.